Stytch offers user impersonation functionality that allows you to log into your application as a specific end user in order to troubleshoot and debug securely.Documentation Index
Fetch the complete documentation index at: https://stytch.com/docs/llms.txt
Use this file to discover all available pages before exploring further.
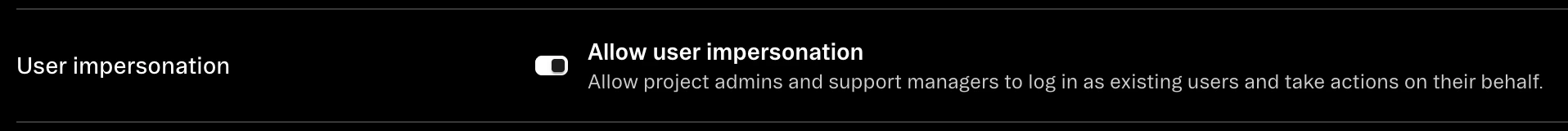
Enabling user impersonation for your Stytch project
User impersonation is disabled by default for each of your Stytch projects. In order to enable it, a member of your team with the Admin role in the Stytch Dashboard should navigate to the Password and User Policies page and toggle on the Allow user impersonation setting. Be sure to click Save after modifying the setting.
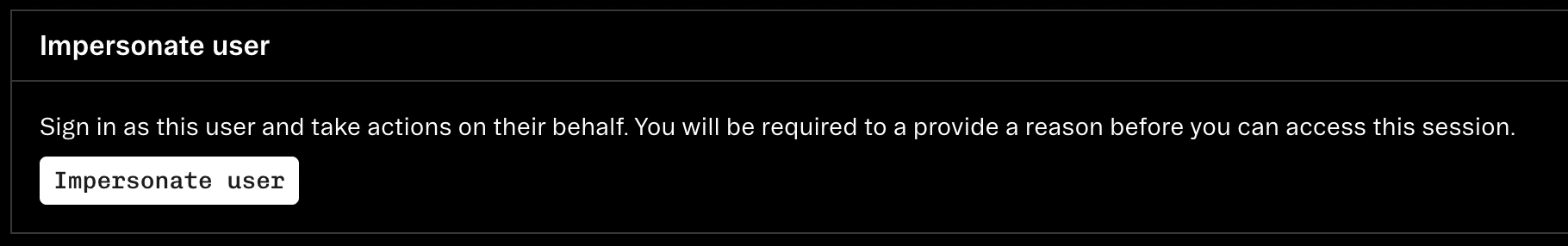
Generating a user impersonation token
Once user impersonation has been enabled for your project, team members with the Admin, Developer, or Support Manager roles can begin the user impersonation flow by selecting the User they’d like to impersonate on the Users page, scrolling down, and clicking Impersonate user.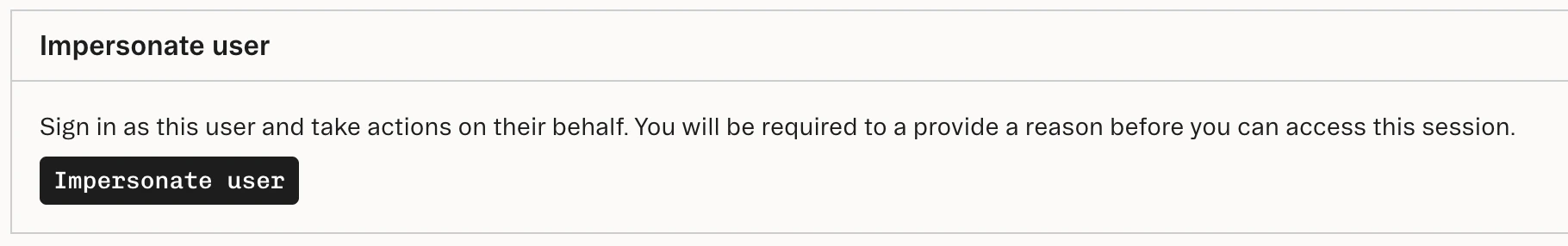
Authenticating a user impersonation token
Your application should then retrieve the impersonation token from your login redirect URL’s query parameters and authenticate it via the Authenticate impersonation token endpoint. If you’re using our frontend JavaScript SDK, you can authenticate the token via the authenticateByUrl method. However, you’ll first need to enable the Authenticate user impersonation tokens setting on the Frontend SDK Configuration page in the Stytch Dashboard. At this point, you’ll receive a new Stytch Session for the target user. Stytch Sessions created through user impersonation always have a duration of one hour, and can be explicitly revoked via the Revoke Session endpoint. They contain a single factor in theirauthentication_factors array of type impersonated that includes the impersonator’s email address.
Here’s an example Stytch Session that was created through user impersonation:
session_token or session_jwt values from the Authenticate user impersonation token response.
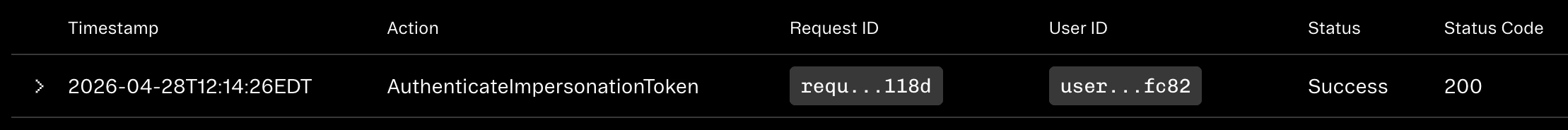
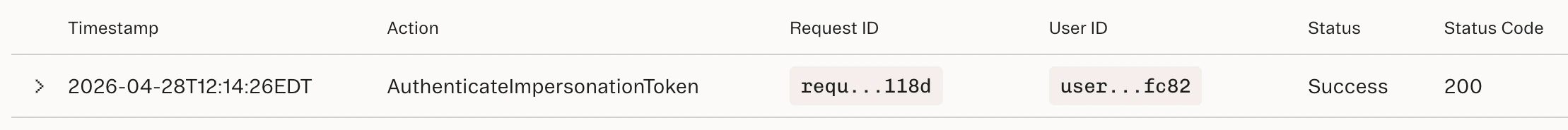
Audit logging
After a user impersonation token is authenticated, you’ll find an event in the Stytch Dashboard’s Activity tab with anaction value of AuthenticateImpersonationToken. This event will contain additional details about the user impersonation,
such as the user_id, the impersonator’s email address, and the reason that the impersonator provided for the
impersonation. If you take advantage of our Event log streaming feature,
the user impersonation logs are available there as well.
direct.user.impersonate whenever
a User is impersonated.