- Decide on the list of countries you would like to block
- Run a shell script to create one Rule for each country to block
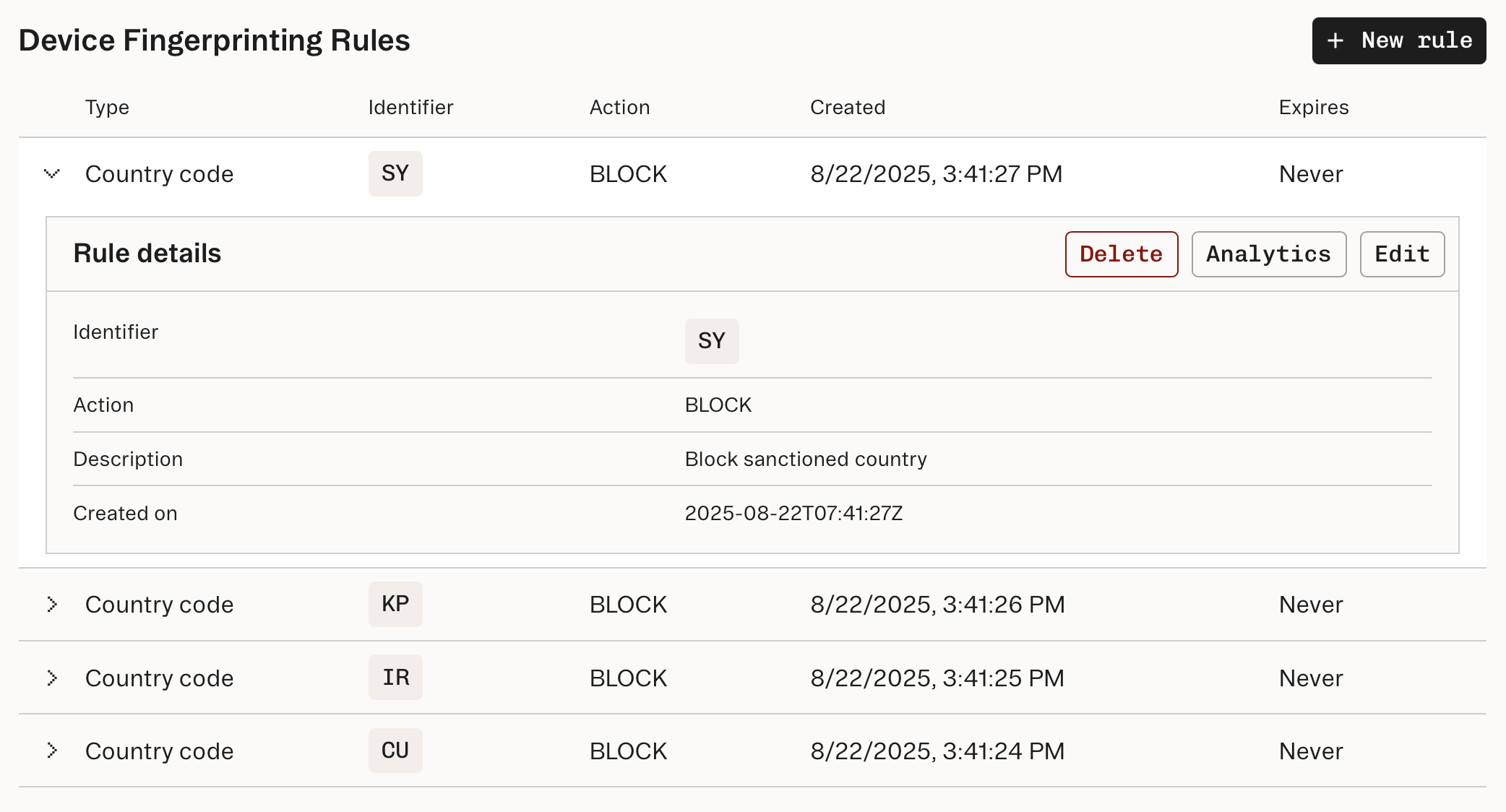
Decide on the list of countries to block
First, decide which countries you want to block. You will need the ISO-3166-1 alpha-2 country codes, likeUS for United States, to set a country-based Device Fingerprinting Rule.
Run a shell script to create one Rule for each country
The following shell function enables you to block a single country using the Set Rule API.You can also create Rules with the Stytch Dashboard. Or, use the Stytch SDK to call the Set Rule API.
What’s next?
If you are using Stytch for authentication and use SMS or WhatsApp one-time passcodes (OTPs), you can set country code allowlists to prevent toll fraud to phone numbers in certain countries. In Device Fingerprinting, you can also set Rules based on other characteristics, such asvisitor_id or network_fingerprint. See Set decisioning rules for more information.
