Back to blog
What is SIM-swap scam, and how can you protect your users against one?
Auth & identity
Oct 23, 2023
Author: Gedney Barclay

A SIM-swap scam, also referred to as SIM-swapping, is a type of account takeover attack that specifically targets someone’s phone as a way to get access to their online accounts. SIM-swapping is notable because unlike many account takeover attacks, it specifically targets a something-you-have authentication factor – namely, verification codes sent to your phone by a call or text.
As multi-factor authentication becomes increasingly commonplace for web applications, understanding how a SIM-swap scam works, and how to protect you and your customers against it are increasingly important for online applications.
Remind me: what is a SIM card?

The SIM in SIM card actually stands for subscriber identity module, which is apt – the SIM card in your phone contains the chip that identifies your phone number with your physical device. It’s what enables you not only to use your smartphone as a computer – to access the web, send emails, use apps – but to make and receive phone calls and critically, to send and receive text messages.
For our purposes, it’s also important to note that your mobile phone carrier has the power to change the phone number associated with a SIM card through a feature called mobile number portability. If you’ve ever kept your phone number when changing phone providers or needed to replace a lost or stolen phone, you’ve taken advantage of this feature. Mobile number portability means phone numbers are not locked to a specific SIM card, but are in fact portable.
It’s this mobile number portability feature that enables SIM-swap attacks to happen.
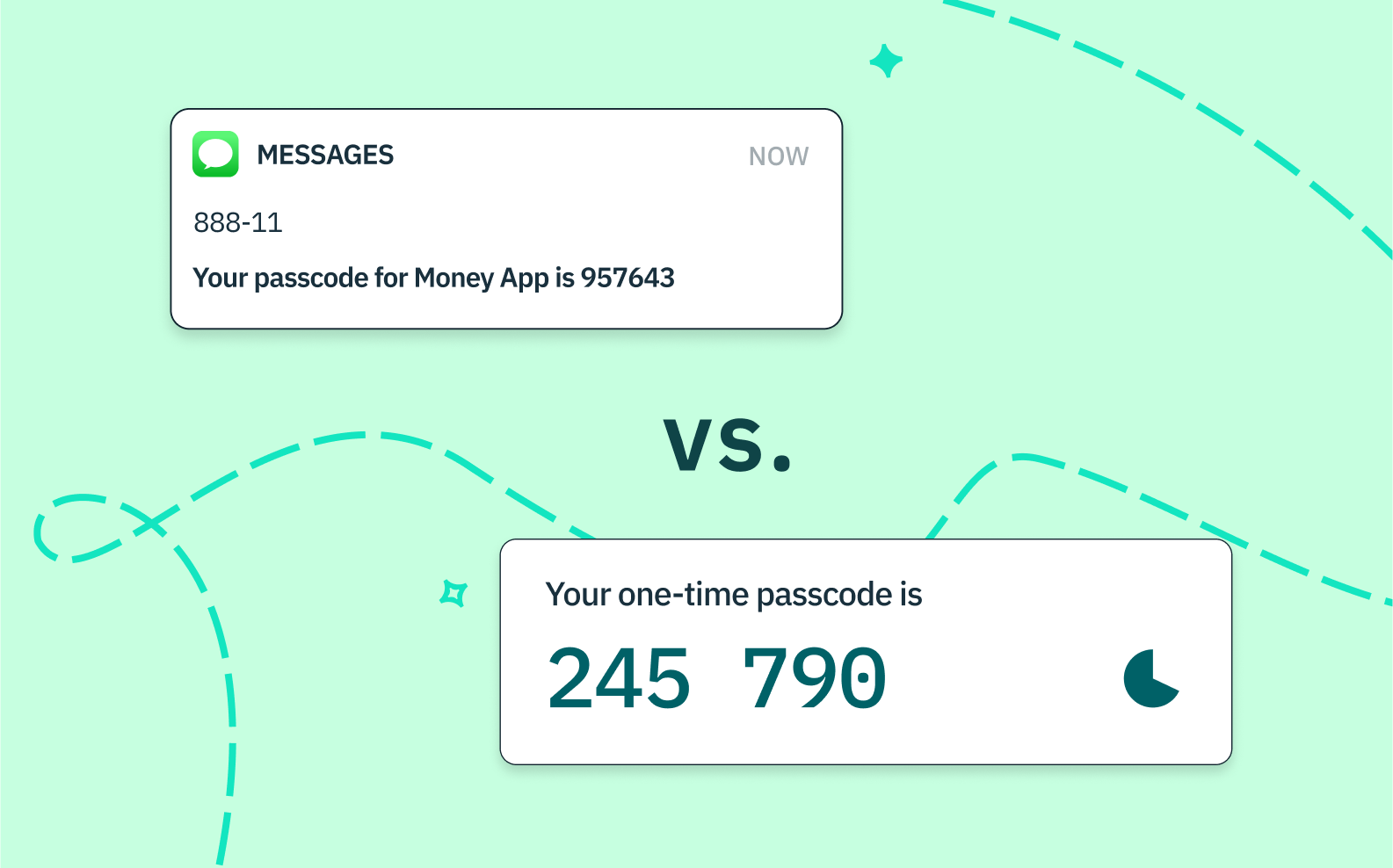
And…what are SMS one-time passcodes (SMS OTP)?
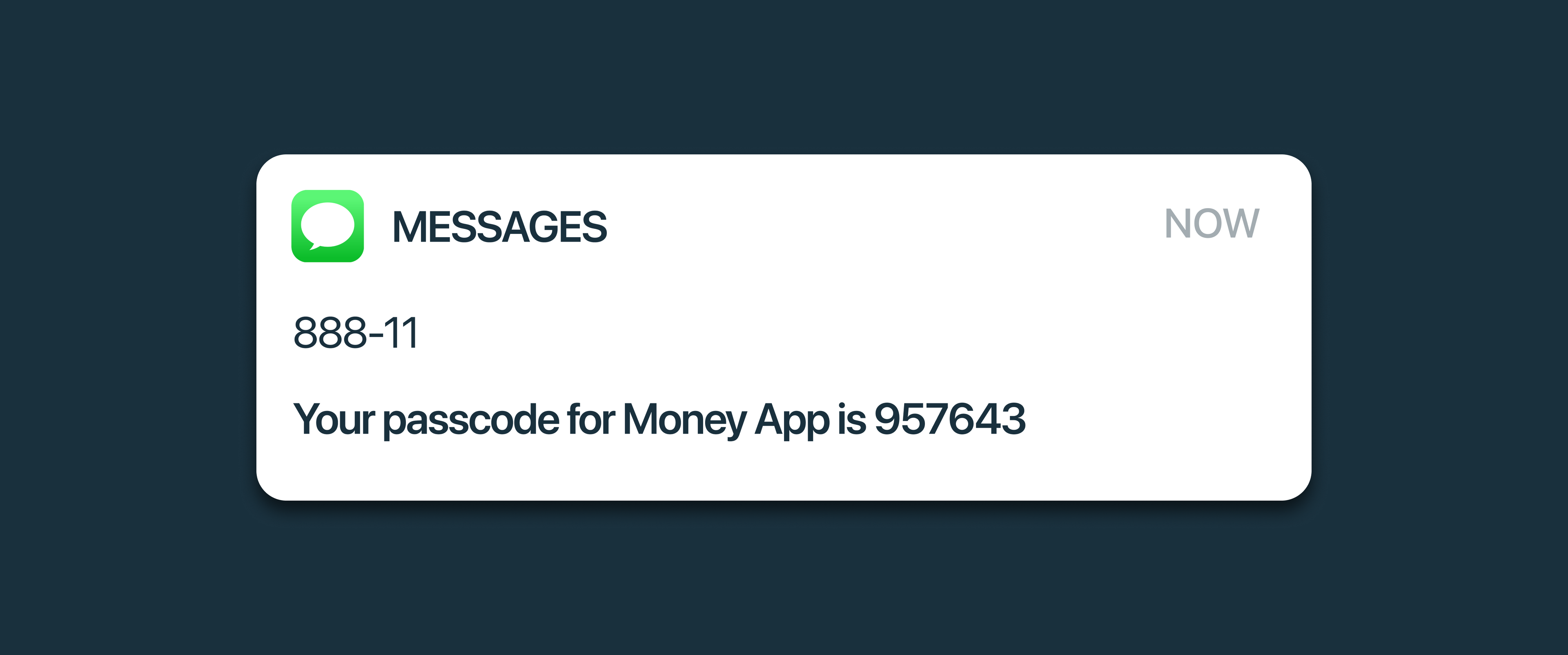
SMS one-time passcodes, (or SMS OTPs) are security codes that are automatically sent to a user’s phone number upon a signup or login attempt. They typically contain a randomly generated string of numeric or alphanumeric characters that a user must input to verify their identity and gain access to or carry out sensitive actions within an app or website.
As the name suggests, a one-time passcode can only be used once — that is, for a single authentication event. After a given code is entered, it is invalidated and cannot be used again.
While in the case of SIM-swapping we’re focused on SMS OTPs (and in some rare cases OTPs that are received through a phone call) it’s worth noting you can also receive OTPs via other services like email or WhatsApp.
Why SMS OTPs are popular
To understand why SMS OTPs are a cybersecurity attack vector, it’s helpful to understand why they’re currently such a popular form of user authentication.
1. Something-you-have
As mentioned above, SMS OTPs are a something-you-have type of authentication. This means that rather than verifying something that you know (like a password) or something that you are (via a biometric reader) the SMS OTP verifies that the user has access to a personal device. Passwords and something-you-know factors are notoriously easier to hack than other factors, so SMS OTPs protect applications from some of the lowest hanging fruit in the fraudster’s arsenal.
2. Versatility
SMS OTPs can be used as a primary or secondary authentication factor, though they’re most commonly used as a secondary one in multi- or two-factor authentication. This means that when someone attempts to log into an application with a password or an email magic link, your app can get additional assurance the user is who they say they are with a second auth factor.
3. Accessible
Unlike some more sophisticated or expensive authentication factors like YubiKeys or passkeys, SMS OTPs are accessible to anyone with a SIM card – you don’t even have to have a smartphone. They’re a great additional auth factor both for any mobile application because the phone is already in the user’s hands. Simultaneously they’re great for applications whose users may not typically have access to other forms of authentication (embeddable magic links, email OTPs, authenticator apps, etc.).
Why are these advantages important to understanding SIM-swapping?
As we’ll see, though SIM-swapping is a bit more labor intensive and less scalable than other forms of account takeover, part of what makes it alluring is the popularity of the SMS OTP itself. Were SMS OTPs less popular among applications, SIM-swapping would be far less tempting as an attack vector.
How does SIM-swapping work?
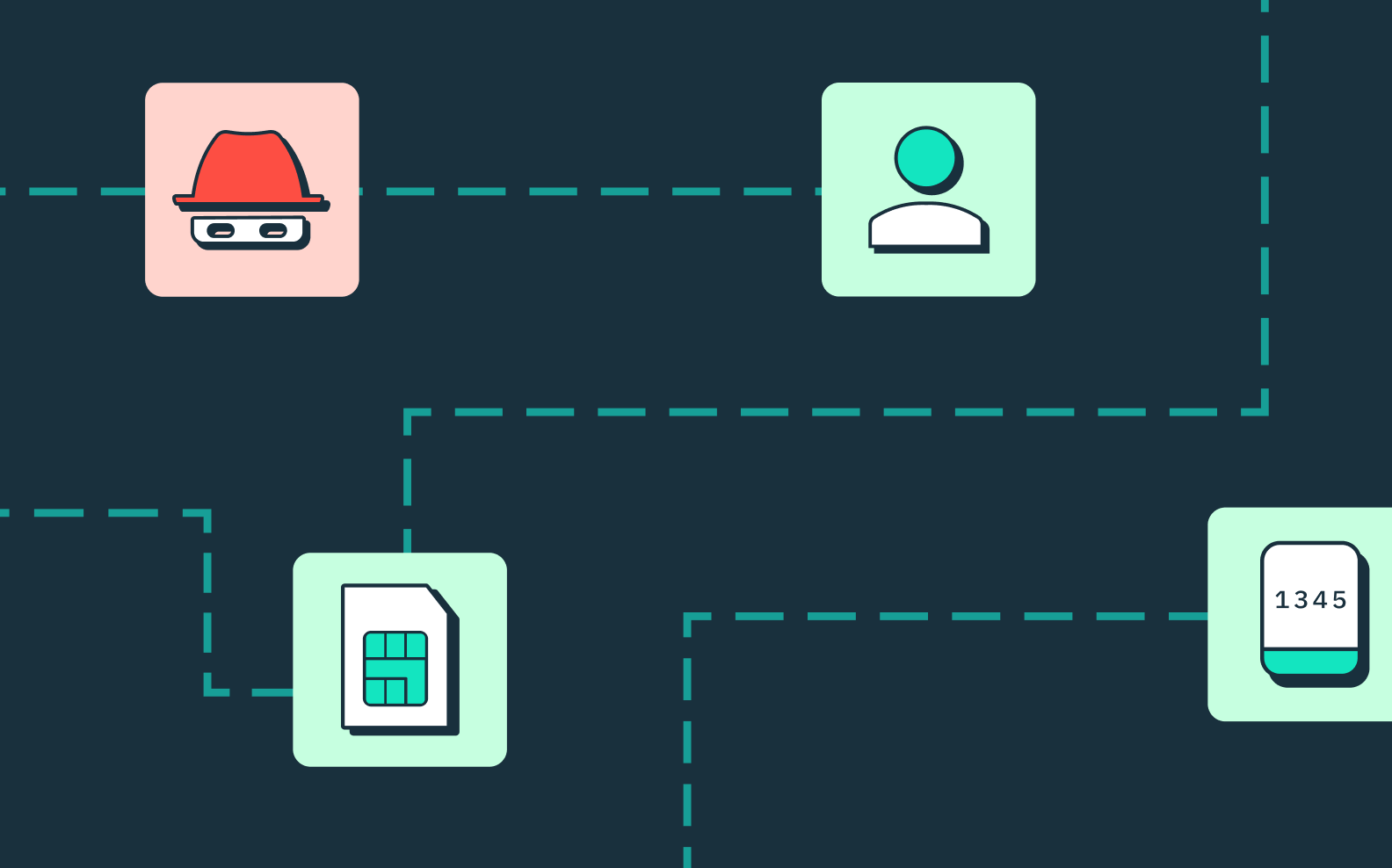
The end goal of SIM-swapping is to gain remote access to a person’s SIM card, and any SMS OTPs they may receive. Typically, fraudsters do this through a combination of phishing and social engineering, both of their target and of their target’s mobile carrier.
Let’s take a look at a SIM-swap attack step-by-step.
1. Obtain personal details
In order to successfully carry out SIM-swap fraud, fraudsters need some personal information about their victim(s). They typically obtain this through phishing emails (which target large groups of people at scale), buying already compromised credentials or personal information.
Note that scammers these days are getting trickier – many are using their targets’ social media accounts to gain personal information. This often involves the fraudster creating fake social media accounts and trying to get their target’s personal info through private messages, perhaps feigning romantic interest or promising alluring business deals. And if they’ve already successfully gotten access to the SIM-card and/or social media accounts of someone you personally know, they will use those accounts to try to get you to reveal personal information by leveraging the higher degree of trust you’re likely to have in known contacts like friends or family.
2. Contact target’s mobile carrier
While phishing or purchasing sensitive information can be done at a fairly large scale, this next step is a little harder to do at a mass level. Once they have a target’s information, the fraudster usually has to call their target’s mobile carrier and convince them that:
- They are the target
- Their SIM card has been lost or stolen.
This is where the personal information phished or purchased comes in handy – to confirm the caller is in fact the owner of the account (which they’re not!) mobile carriers may ask for an email address, physical address, or other types of identity verification. Depending on how successful the fraudster was in obtaining information on their target, if they answer these questions successfully they can successfully convince the mobile carrier to switch their target’s phone number to a SIM-card that they control.
3. Account takeover
With personal information on hand and control of their target’s phone number, the fraudster can now likely take over online accounts from their target even if those accounts are protected by two-factor authentication. Any SMS directed to their target’s phone number, including SMS OTPs, will go directly to their SIM-card. To boot, they now control all incoming and outgoing phone calls from that person’s phone number. In other words, they have effectively swapped their SIM-card for their target’s.
Assuming the information they phished or purchased included one or more usernames and passwords, they have enough information to gain access to financial accounts, bank accounts – even those protected by two-factor authentication.
Want unphishable MFA for your app? Switch to Stytch.
Pricing that scales with you • No feature gating • All of the auth solutions you need plus fraud & risk
SIM-swapping in the news
Perhaps the most well-known SIM-swap attack occurred in 2019 against former Twitter CEO Jack Dorsey. As a high net-worth individual and someone with a lot of publicly available personal details, Dorsey was a prime SIM-swap target. SIM-swap attacks both need to be higher reward to be worth the hacker’s high touch effort and often rely on publicly available personal information – Dorsey checked both those boxes.
Signs of a SIM-swap attack

So how will a user know know if they’ve been the victim of SIM-swap fraud? There are often a few key signs:
1. They can’t make phone calls or send text messages.
If your user suddenly can’t make phone calls or text messages, or if they’re not receiving calls or texts, that could be a strong indicator of SIM-swapping. Of course, users should make sure there aren’t any obvious explanations like their phone accidentally got switched into Airplane Mode, or they’re traveling through an area of notoriously poor reception! But once other factors have been eliminated, it’s worth reaching out to their phone carrier.
2. They don’t have phone service.
Relatedly, if a user’s mobile phone consistently and very suddenly has no service, especially in locales where they previously did, it may be worth reaching out to their phone carrier in these instances.
3. Unrecognized activity on your social media accounts.
Social media accounts are a common account target for fraudsters, because they can leverage them to phish and scam other people in their target’s network. If someone notices activity on their social media accounts that wasn’t them, they’ve likely been hacked in one way or another. If that activity is present with other indications of SIM-swapping, it’s a good time to reach out to their mobile provider to see if their phone number has recently been moved to another SIM card.
4. Their mobile carrier notifies you that your number has been moved to a new SIM-card.
Perhaps one of the most obvious signs of a SIM swap, one should take note if their cell phone carrier contacts them notifying you of a SIM swap that they did not initiate.
5. Unrecognized activity on bank or other financial accounts.
Typical of any kind of fraud or account takeover, if someone notices any unusual activity on their bank or financial accounts, it’s definitely likely a sign that some kind of fraud or hacking has taken place.
Protecting against SIM-swap scams

To prevent SIM-swapping, there are two main areas where companies and individuals can take precautions: on the individual, behavioral level, and at the application-wide, security infrastructure level.
Behavioral precautions against SIM-swap attacks
- Be wise to signs of phishing and social engineering: Don’t trust emails from people or organizations you don’t recognize, especially if those emails come with calls-to-action (CTAs) to click on links, fill out forms, or send back personal information. While there are often telltale signs these come from a fraudster like typos or an email address that doesn’t correspond to the sender’s information, also be wary of CTAs that are conjuring up a sense of urgency, danger, or big reward (“Send me your bank account info so you can claim your prize!” etc. etc.).
- Use unique, strong passwords: In order to SIM-swap, fraudsters first need to be able to obtain your personal information. In addition to phishing or social engineering, they may also try to obtain that information through various kinds of brute force attacks.
- Protect your personal information: Unless you’re a professional social media influencer, you may want to consider keeping your social media accounts private. Many fraudsters will closely follow social media accounts of their targets to try to glean personal information like their birthday, pets’ names, birthplace, address, etc.
- Always use two-factor authentication: Even though second auth factors like SMS OTP are vulnerable to certain kinds of attacks, they’re still a crucial protection between individual users and hackers. Any point of resistance or additional labor you can add to their plate, the less likely they are to pursue you. If the possibility of SIM-swapping makes you wary of SMS OTP, consider other 2nd auth factors like passkeys, time-based one-time passcodes (TOTPs), or physical hardware keys like YubiKeys.
Application-wide protections against SIM-swapping
SIM-swap fraud may be on the rise, but so is the use of more secure authentication methods. Some of the best that can protect your company and your customers include:
- Incorporate step-up authentication: If the day-to-day transactions on your app may not immediately implicate your users’ personal information, you might not want to require several authentication methods just to get in. BUT, certain actions like updating payment information or passwords are more sensitive, and could benefit from added protection. Step-up authentication is a form of MFA that is only triggered for more sensitive account-related actions. By requiring an email OTP or a biometric only for certain transactions, you keep your users safe without imposing undue friction.
- Upgrade to more modern authentication methods: With newer auth methods like TOTPs (also called authenticator apps) and passkeys now available, it’s a great moment to encourage users away from less secure methods like passwords and SMS OTP and towards these more future-forward, secured approaches. You can start by giving them additional options for their primary and secondary authentication methods, offering additional education, etc., to see how these newer methods perform with your users. Which authentication methods you choose will likely depend on your use case – do most of your users have access to a smart phone? Are they familiar with or likely to adopt newer technologies? The more you give them options now, the more easily you’ll be able to wean them off of these less secure methods in the long run. Because remember: SIM-swapping isn’t a vulnerability merely because SIM cards are vulnerable, they’re a vulnerability because passwords are also highly breachable. It’s the combination of passwords’ weakness as a primary auth factor with SIM-swapping as a secondary that make them both prime targets of fraud.
- Invest in fraud prevention tools: Because SIM-swapping happens in conjunction with other kinds of attacks targeting personal information, applications can benefit from fraud prevention measures like device fingerprinting or CAPTCHA that help detect and block suspicious behavior before they even get to the point of requesting an SMS OTP. Additionally, products like Stytch’s Device Fingerprinting can generate device identifiers that can be used defensively against SIM-swapping attacks even after the phone number has been swapped. For example, if an application adds a Stytch device fingerprinting checks to either their OTP pin submit or request otp PIN endpoints, that application could actually detect a sim-swap attack before the OTP is transmitted or allowed to be used for access by the fraudster, because the fraudster’s physical device characteristics/versions/etc., would likely differ from the original user whom they targeted.
Protect your users with authentication and fraud protection from Stytch
Stytch is unique in the world of identity platforms in that we offer both a wide range of passwordless authentication solutions alongside a robust set of fraud prevention tools. Get started building for free, explore our docs, or get in touch to schedule a demo today.
Authentication & Authorization
Fraud & Risk Prevention
© 2020-2026 Stytch. All rights reserved.