Back to blog
Out-of-the-box: User linking and provider failover with Stytch
Product
Apr 11, 2024
Author: MB Crosier
Many of our engineers built authentication systems elsewhere before joining (or, in Julianna’s case, starting) Stytch. And as a result, our team knows firsthand the pain and frustration of many of the hidden steps you have to take to get set up and then to ensure a secure and reliable auth setup going forward.
In this post, we’ll walk through two of the common hassles of auth setup that Stytch takes care of for you:
Secure User Account Linking & Deduplication
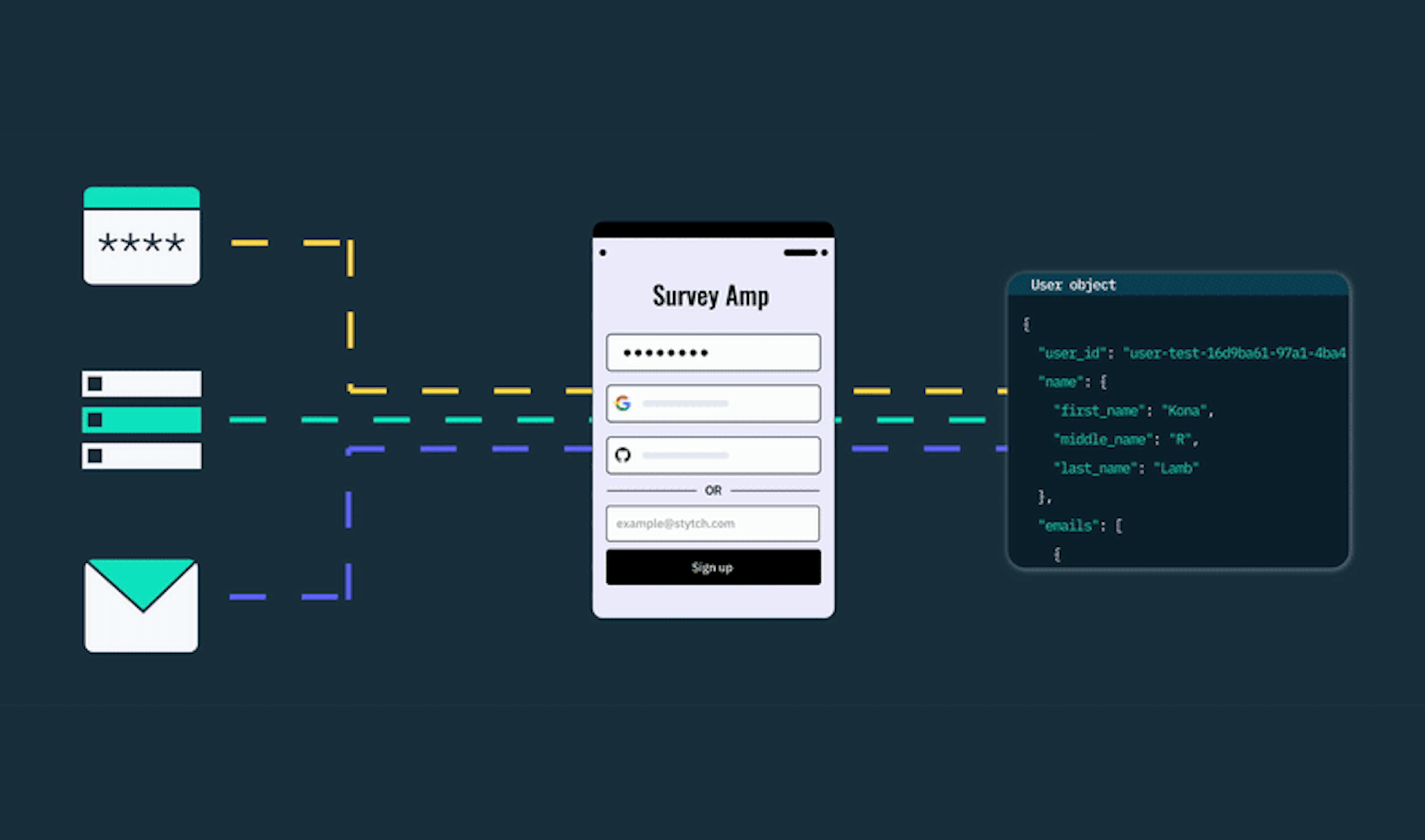
Another important infrastructure consideration that Stytch handles for you out of the box – with no additional setup required – is secure account deduplication.
In other words – Stytch ensures that if a user signs up with username and password, but then tries to login with Google OAuth, they don’t accidentally create two separate unlinked accounts. And, the linking happens securely and requires email verification – since insecure account linking can lead to account takeovers.
If you use another solution like Auth0, this functionality does not exist out of the box, leaving you with three options:
Option 1: Allow users to create a new account with each factor
For example, a user could create one account by logging in with username and password, and then create a separate account by logging in with Google OAuth..
This is a great way to get an influx of support requests where confused users think all their account data has disappeared (and also, a good way to get a lot of duplicate / phantom accounts that will never be used).
Here’s an example where a company opted to not link accounts, but instead wrote out a support help article as a resource for users who were confused and struggling to log in. It’s a solution, but it’s not a particularly graceful one.
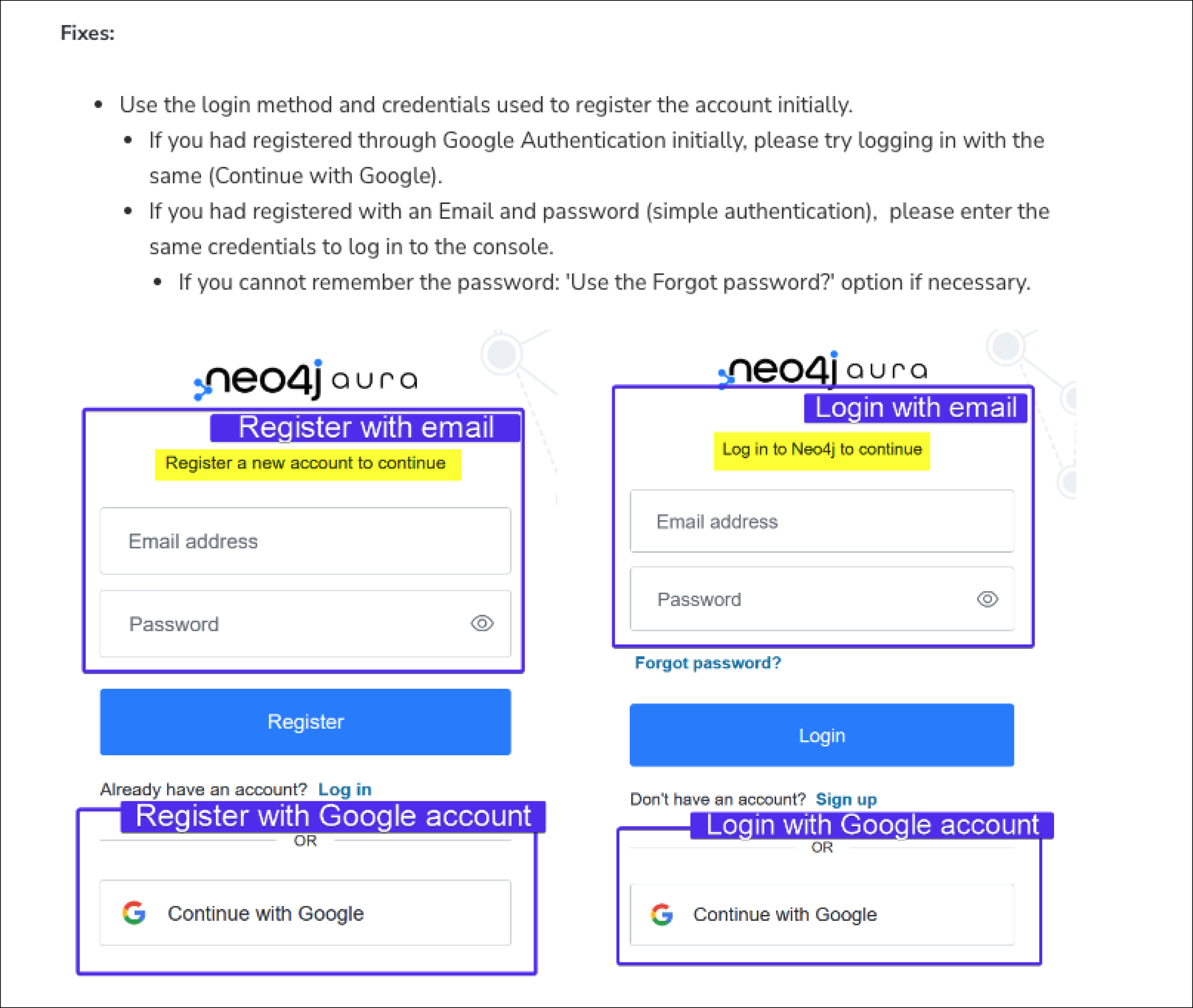
Option 2: Block users from logging in with any factor except the original one they used
This prevents duplicate accounts, but is a bad user experience. No one wants to hit a screen like this, and users may get frustrated and drop off (or, contact support, which is expensive).
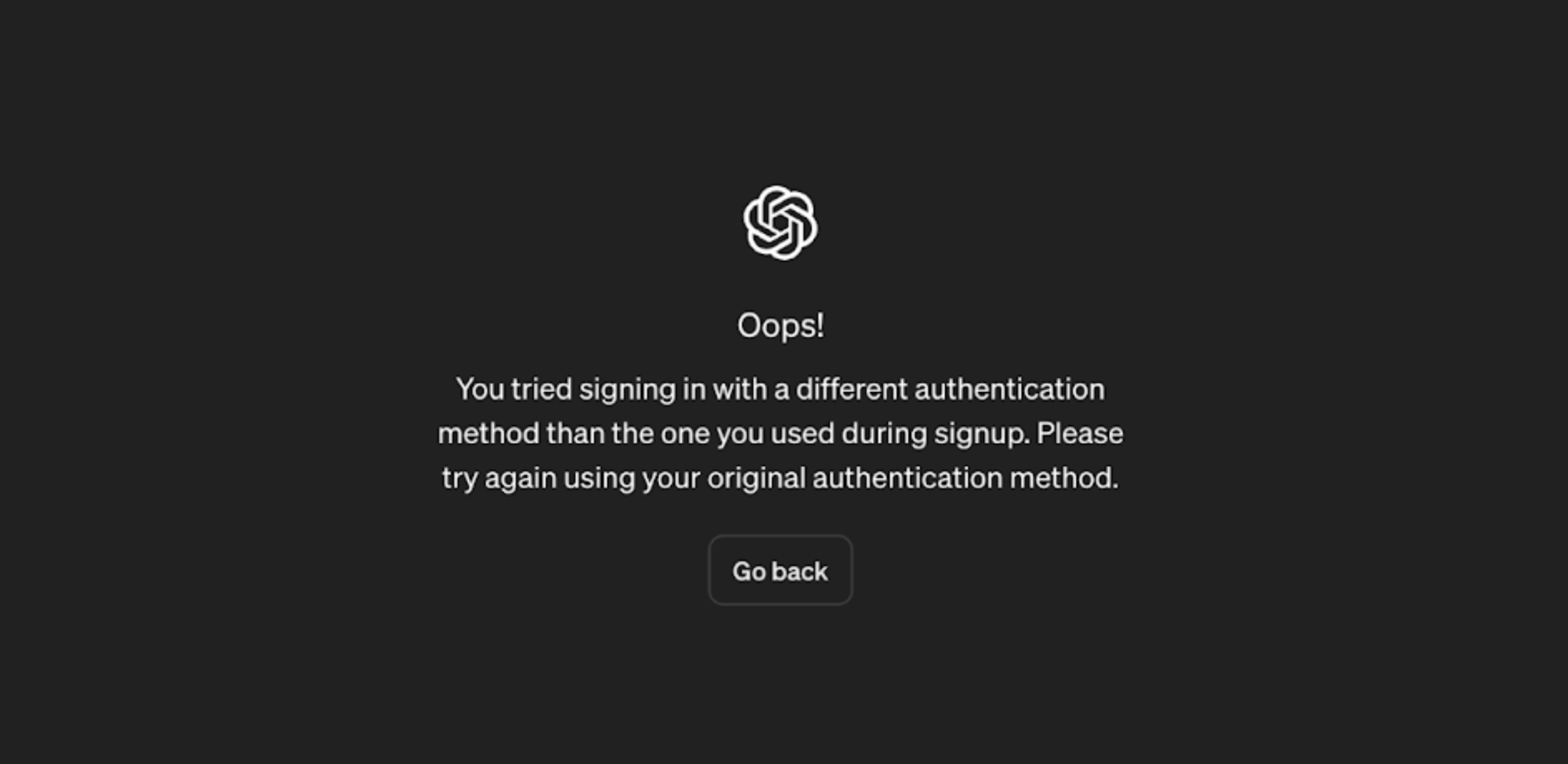
Fun fact: there are now so many users asking questions online about why they can’t log into OpenAI account with a different authentication method that competitors are using it as SEO-bait.
Option 3: Write glue code to link accounts
For Auth0, this means either adding an extension, writing a custom Auth0 Action or Auth0 Rule, and availability may vary based on your Auth0 implementation. Linking accounts is not to be taken lightly, as it has meaningful security implications.
Option 4: Use Stytch (aka none of the above)
With Stytch, none of these workarounds are necessary. Account linking happens automatically, but with consideration to the many nuances of what information is shared and verified by each login method.
For example, since Microsoft OAuth doesn’t verify email ownership, Stytch does not merge Microsoft OAuth logins with, for example, magic link logins, automatically without an additional verification step. These behaviors are outlined in the Stytch docs by provider for reference.
You can try this out on stytch.com/start-now; magic links and Google OAuth both verify your email, and both take you to the same place.
SMS & Email: Sending and Provider Failover
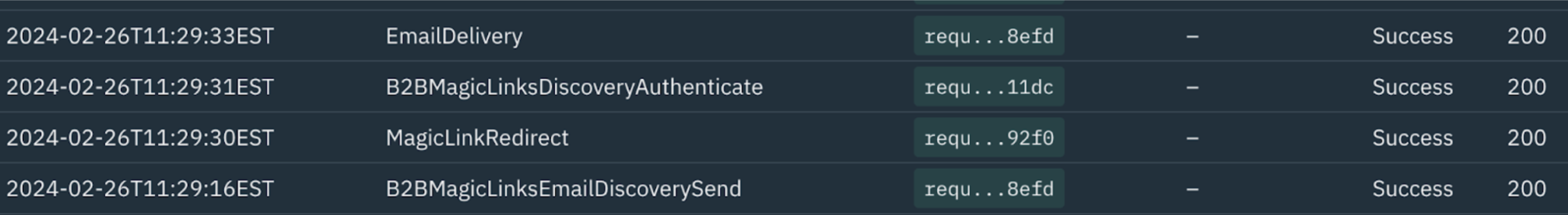
Unlike a lot of other auth providers, Stytch handles sending emails and SMS messages for you, sending one-time passcodes and magic links directly through 3rd party services like Twilio, MessageBird, SendGrid, and more.
Emails and US/Canada OTPs are offered at no cost; international OTP costs are passed through at the costs incurred from 3rd party providers. In practice, this means huge time savings in setup and negotiation – rather than configuring multiple providers, grabbing API keys, drafting custom templates and optimizing them for deliverability, Stytch allows you to immediately start sending messages to users.
And perhaps even more importantly, Stytch also handles provider failover – ensuring that multiple SMS and email providers are available, so if one is experiencing an outage or latency, your critical login emails and one-time passcodes are still getting delivered.
This allows you to spend less time worrying about deliverability issues, or optimizing your email or SMS templates to avoid being marked as spam (there’s more to this than you might expect!).
Email delivery from third party providers is also included in Stytch’s event logs for observability purposes; you can learn more about message deliverability at Stytch in the docs.
The bottom line: time savings
In summary, by handling key configuration steps, like SMS/email delivery and account linking, Stytch allows you to more quickly and easily get up and running, and then ensures your users can log in reliably as you scale.
If you want to try it for yourself, you can get started with Stytch free today!
Build auth with Stytch
Pricing that scales with you • No feature gating • All of the auth solutions you need plus fraud & risk
Authentication & Authorization
Fraud & Risk Prevention
© 2020-2026 Stytch. All rights reserved.


