Back to blog
What is unphishable MFA?
Auth & identity
Oct 24, 2022
Author: Stytch Team

In the world of authentication, there are many options when it comes to verifying a user's identity — but they’re not all created equal. For instance, passwords are easily compromised through common hacking methods like brute force attacks and credential stuffing because they’re often easy to guess or reused across multiple accounts.
This is one reason many security-minded organizations are adopting multi-factor authentication (MFA) — which requires additional authentication factors like email magic links or biometrics — as the standard for identity verification. Still, there are many possible forms and variations of MFA, and some offer better security than others. In this article, we explore why some MFA flows fall prey to phishing attacks, explain what unphishable MFA does differently, and break down why it’s the best option for protecting your apps and data from malicious actors.
What is phishing?
To understand the importance of unphishable MFA, it’s important to first understand the dangers of phishing scams. Phishing is a form of social engineering. Rather than targeting vulnerabilities in computer systems or hardware, social engineering attacks aim to exploit the human component of an organization or user. They deploy deceptive tactics that trick people into divulging personal information or granting access to a sensitive database through fraudulent messages and/or malicious links. This might look like an email from an unknown contact containing a link that promises some kind of reward or to fix a “problem” the user isn’t aware of.
But not all phishing attacks are so overtly suspicious.
For example, password phishing scams frequently mimic legitimate password reset emails and are a popular way to gain access to user credentials. MFA is designed to thwart these scams by employing additional layers of security to verify a user's identity. With MFA, even if a user’s credentials are compromised, a hacker would have to bypass those extra security measures to gain access to the system, making a successful breach more difficult.
Is MFA phishable?
The short answer is, yes. Certain forms of MFA are phishable. Any MFA factor that is tied to a user’s personal phone number or email address—like an SMS one-time passcode, email magic link, or voice authentication—can be compromised by a determined hacker.
Emails are a very common vector for phishing attacks. Hackers use malicious email links that direct users to fake landing pages and proxy servers that record any credentials and one-time passcodes users enter. The hacker can then plug in that information on the back end to gain access. This is also known as a man-in-the-middle (MitM) attack. With SMS, phishing can get a little more sophisticated, but similarly involves a phisher somehow convincing a user to share a one-time passcode (OTP) or other sensitive information that the hacker can use to gain access to their account.
Interested in unphishable MFA? Try Passkeys from Stytch.
Pricing that scales with you • No feature gating • All of the auth solutions you need plus fraud & risk
How does unphishable MFA work?
Unphishable MFA is a multi-factor authentication flow that cannot be compromised by any of the tactics mentioned above. Relying on asymmetric or public-key cryptography, this form of authentication provides the highest level of security. Asymmetric cryptography encrypts valuable data — in this case, access to a server — using a public key and a private key. The public key is stored on the server, while the private key can only be unlocked by the user. Once unlocked, the private key sends a personalized message to the public key, providing the user with access.
This cryptographic foundation can be paired with different authentication factors in an MFA flow, allowing users to verify their identity securely in the following ways:
- Security key-based authentication (something you have) After inputting their credentials or code, a user is asked to provide a physical security key. When inserted into the user’s device, the private key is triggered, and the user is granted access to the server.
- Biometric authentication (something you are) After inputting their credentials or code, a user is authenticated using a physical feature like a fingerprint, retinal scan, or facial scan. The private key is then triggered, granting access to the server.
How does unphishable MFA prevent the most persistent hackers?
This approach offers protection against phishing attacks in four critical ways:
- It requires physical interaction Because users must engage physically with the device they’re requesting access from, they can’t be compromised through remote attacks by a hacker, bot, or trojan.
- It uses unique keys every time An important characteristic of asymmetric cryptography is that it generates unique keys for each individual service, ensuring no two keys are reused across multiple sites. And, because only the public-facing key is stored, there’s no way for hackers to know which sites or services a user is registered on.
- Biometrics aren’t saved on the network Similarly, unlike passwords, a user’s biometrics aren’t stored or sent over the internet. They’re only used to trigger the private key.
- Access is bound by origin Only the real site can authenticate the private key, helping protect users against man-in-the-middle attacks.
Taken together, these factors explain why this type of MFA is referred to as “unphishable.” And they’re why incorporating unphishable MFA into your website or app is the best way to prevent cyberattacks and safeguard your and your users’ data.
Fight back against phishing
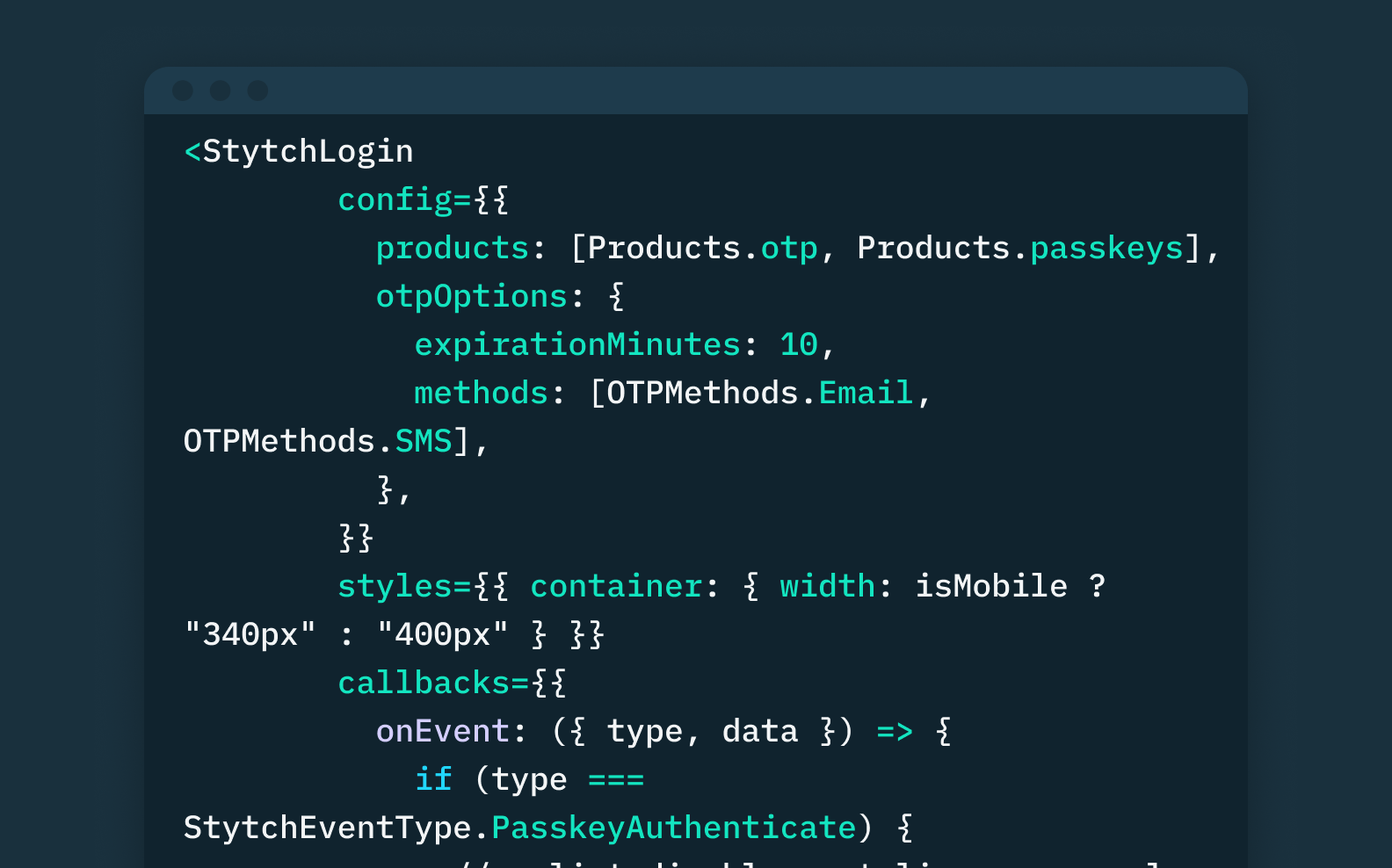
For Stytch, security comes first. Sign up for a free account, and discover our unphishable, easy-to-integrate solutions for passwordless authentication. Sign up today.
Authentication & Authorization
Fraud & Risk Prevention
© 2020-2026 Stytch. All rights reserved.